Hi,
Firstly, apologies if what I am writing here is redundant as I did search and see other entries for DNSCrypt, but none really addressing the issue I am having. Apologies also if this is outside of the scope of this PiHole forum, but I am at my wits end trying to get this figured out.
Now, for the issue. I've followed the guide posted here several times (the latest of which was a complete OS re-install) to a T and have gotten absolutely nowhere.
I have previously gotten to the point where I at least had DNSCrypt running separately from PiHole (and was able to ping and resolve using command line), but it seems like presently it's failing out with some kind of error, but I have no understanding on how to figure out what the error is or how to fix it.
When running "sudo systemctl status dnscrypt-proxy" I get:
● dnscrypt-proxy.service - Encrypted/authenticated DNS proxy
Loaded: loaded (/etc/systemd/system/dnscrypt-proxy.service; enabled; vendor preset: enabled)
Active: activating (auto-restart) (Result: exit-code) since Mon 2018-05-14 13:18:05 PDT; 24s ago
Process: 1248 ExecStart=/opt/dnscrypt-proxy/dnscrypt-proxy (code=exited, status=255)
Main PID: 1248 (code=exited, status=255)
May 14 13:18:05 Corpus_Colossus systemd[1]: dnscrypt-proxy.service: Failed with result 'exit-code'.
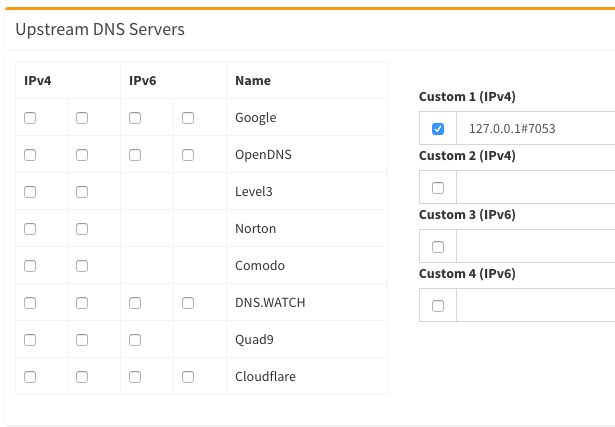
The other thing, which I am finding separately odd, is that I moved to the FTLDNS branch of PiHole explicitly in hopes of finding the "Local DNS server on custom port" option in the admin interface, but it is still not there (and I did confirm that I was on latest FTL for both core and admin console). The only thing I can think of is this option isn't available if the DNSCrypt service isn't running, but otherwise its absence is baffling to me as I've seen screenshots where it exists.
To help save the sanity of anyone trying to help, I'm not super familiar with *nix standards and practices, but on this latest attempt I made sure to make duplicate original files and document all changes that I made before editing, so I at least have that going for me.
Also, because I am a novice, please don't assume that I will know about ANY step or command that is not explicitly called out. I can follow instructions no problem, but I'm in the early stages where you don't know what you don't know, if that makes sense.
Thank you very much for your time/insight!